Law enforcement agencies handling Criminal Justice Information face strict data security requirements under CJIS Security Policy. Scene documentation, investigation records, and evidentiary materials must reside in compliant infrastructure with auditable access controls and encryption standards. The mapping platform you deploy determines whether your 3D documentation workflow meets FBI CJIS requirements or creates audit findings that jeopardize funding and information sharing agreements.
Contents
- CJIS Security Policy requirements for cloud services
- Platform comparison for law enforcement data handling
- FBI audit preparedness and compliance documentation
- State CISO requirements and agency IT coordination
- Incident response and breach notification obligations
- Get a SkyeBrowse quote

CJIS Security Policy Requirements for Cloud Services
CJIS Security Policy 5.9.1.1 governs cloud service providers handling CJI (Criminal Justice Information). Providers must demonstrate: (1) data encryption in transit and at rest, (2) access controls limiting personnel contact with CJI, (3) background investigations for personnel with potential access, (4) security awareness training, (5) incident response procedures, (6) audit logs documenting access, and (7) contractual agreements (CJIS Security Addendum) formalizing compliance obligations.
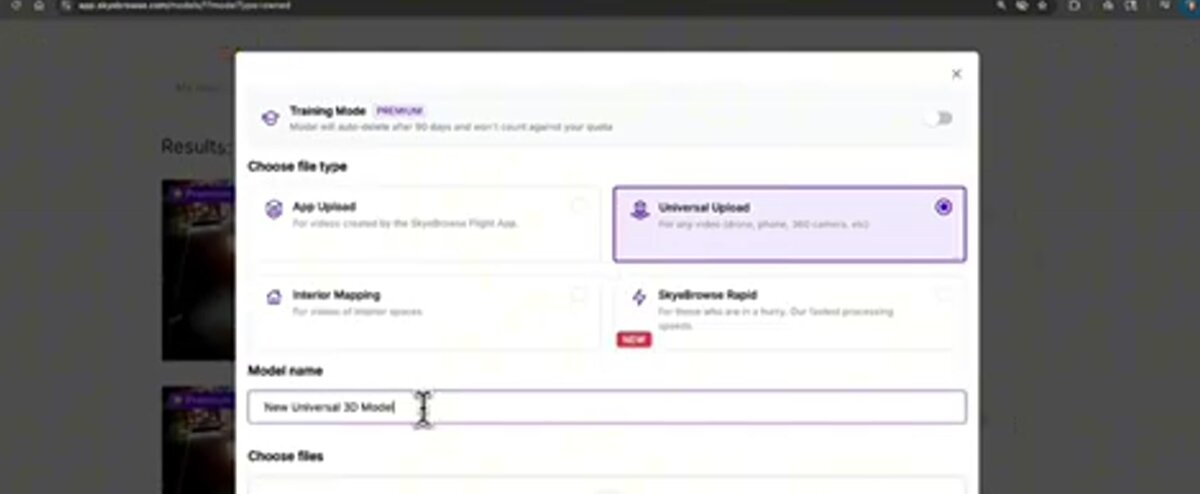
Many cloud mapping platforms operate on commercial infrastructure (AWS, Azure, Google Cloud) that can support CJIS compliance but doesn't guarantee it. Agencies must verify: Is the provider's infrastructure in a CJIS-compliant region? Has the provider executed CJIS Security Addendums? Do processing workflows isolate CJI from non-compliant infrastructure? Are personnel background-checked per CJIS standards?
Platform Comparison for Law Enforcement Data Handling
| Platform Type | CJIS Considerations | Compliance Status |
|---|---|---|
| SkyeBrowse Premium/Advanced (AWS GovCloud) | Operates on CJIS-ready infrastructure, Security Addendum available, access controls, encryption | Compliant when properly configured and approved by state CISO |
| Consumer Cloud Storage (Dropbox, Google Drive, iCloud) | Commercial infrastructure, no CJIS agreements, inadequate access controls | Non-compliant—FBI audits cite this as common violation |
| On-Premise Processing | Agency controls infrastructure, no third-party data sharing | Compliant but requires agency IT resources for processing, storage, and maintenance |
| Generic Photogrammetry Cloud Services | Variable—most lack CJIS addendums, use commercial cloud regions | Presumptively non-compliant without documented CJIS framework |
FBI Audit Preparedness and Compliance Documentation
CJIS compliance audits: FBI and state audit authorities conduct triennial compliance audits reviewing: access control policies, encryption implementation, personnel background checks, security awareness training, incident response procedures, and system usage logs. Non-compliance findings trigger corrective action plans, and serious violations can suspend NCIC access—crippling law enforcement operations.
Cloud service usage receives audit scrutiny. Auditors ask: What cloud services does your agency use? Where do those services store data? Has your CISO approved each service? Are CJIS Security Addendums executed? Do contracts include right-to-audit provisions? Agencies unable to document compliance face findings.
State CISO Requirements and Agency IT Coordination
CISO approval process: State CJIS officers vet technology vendors ensuring FBI compliance requirements are met. Approval processes vary by state but generally require: vendor completes security questionnaire, provides infrastructure documentation (where data resides, encryption methods, access controls), executes CJIS Security Addendum, and submits to state CISO review. Approval timelines range from weeks to months depending on state workload.
Agencies should initiate CISO approval before procurement—purchasing technology that later fails CISO review wastes budget and delays operational deployment. Contact your state CISO early: "We're evaluating 3D mapping technology for crime scene documentation. We're considering SkyeBrowse—have they been approved in our state, or do we need to initiate a vendor review?"
Incident Response and Breach Notification Obligations
Data breach scenarios: CJIS-covered incidents include: unauthorized access to CJI (hacked accounts, stolen devices), accidental disclosure (emailed to wrong recipient, public link sharing), and infrastructure breaches (cloud provider security failures). Agencies must report incidents to state CISO and potentially FBI within defined timeframes (often 24-72 hours).
Cloud service breaches fall into this framework. If SkyeBrowse suffers a data breach affecting agency information, SkyeBrowse notifies affected agencies immediately. Agencies then assess whether CJI was compromised and report per CJIS policy. Contractual incident notification provisions (in CJIS Security Addendum) formalize these obligations—providers must notify agencies promptly enabling compliance with reporting requirements.
ROI: Documentation Efficiency and Cost Savings
Traditional crime scene documentation requires 3-4 hours on-scene with 4-6 personnel (investigators, forensic technicians, supervisors) at total cost of approximately $360-$500 per scene. CJIS-compliant video-based 3D documentation compresses this to 15-20 minutes with single officer smartphone or drone capture, reducing scene documentation costs to approximately $25-$75 (CJIS-compliant Premium/Advanced tier processing).
For agencies processing 200+ annual scenes (collisions, property crimes, outdoor investigations), video-based workflows save approximately 600-700 personnel hours annually, valued at $18K-$28K (at $30-$40/hour loaded officer rates). This efficiency enables reallocating personnel to active patrol, follow-up investigations, or overtime reduction initiatives while maintaining CJIS security compliance throughout documentation workflow.
Get a SkyeBrowse Quote
Law enforcement 3D documentation demands cloud platforms that meet CJIS Security Policy requirements while supporting operational workflows. If your agency needs crime scene mapping, investigation documentation, or training scenarios requiring CJIS-compliant cloud processing and storage, SkyeBrowse provides the infrastructure compliance, security addendums, and audit documentation that FBI CJIS requirements demand.


